The security of the BINETX PTM information software System can be reviewed from several points of view - as a technological realization, as an integration solution and as a set of user options for managing and controlling the actions and operations of the System. The present material is more practical and user oriented. For this purpose, the following issues are addressed: ✓How to identify System users and how they receive access rights to System resources and functions; ✓What options for management and control options there are on the user operations; ✓How to ensure security, monitoring and control when executing financial operations in PTM; ✓What tools for active incident management PTM offers.
Brief historical reference: In 2015 BINETIX presented on the Bulgarian market the first fully automated and integrated platform for Management, Control and Security of information in compliance to the Bulgarian legislation and specifically to the requirements of the LMAML and the LMAFT. The technology is embedded in the latest versions of BINETIX PTM also in relation with the entry into force of the European Parliament's Personal Data Protection Regulation 2016/679 (GDPR). When controlling the financial operations and performing reconciliations in BINETIX PTM, security checks on individuals are carried out in strictly accordance to the lists of suspicious persons officially published by SANS. The result of these checks generates incidents and is a feature of the client profile. |
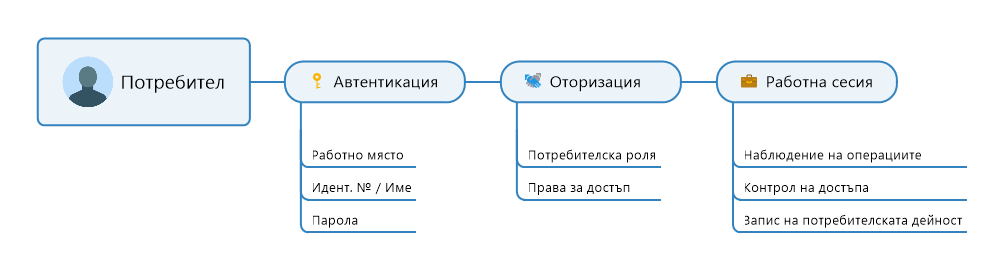
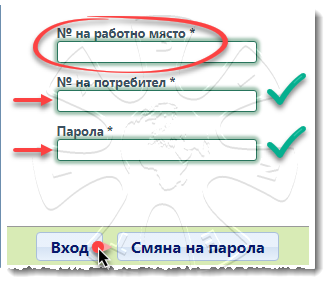
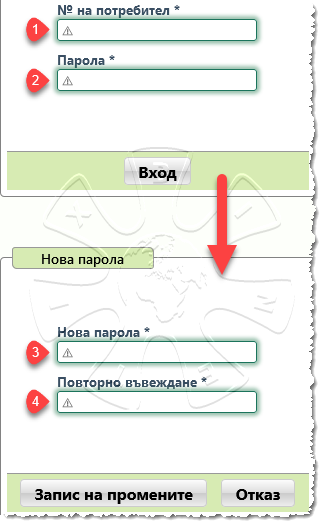
 Identification of the working place
Identification of the working place
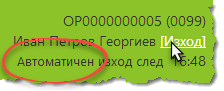
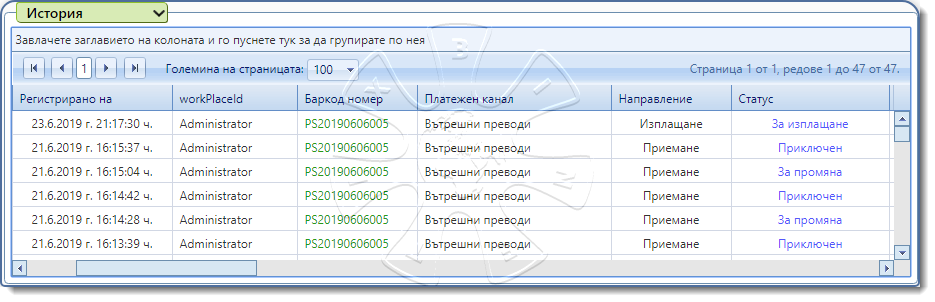
 Management and monitoring of user operations
Management and monitoring of user operations
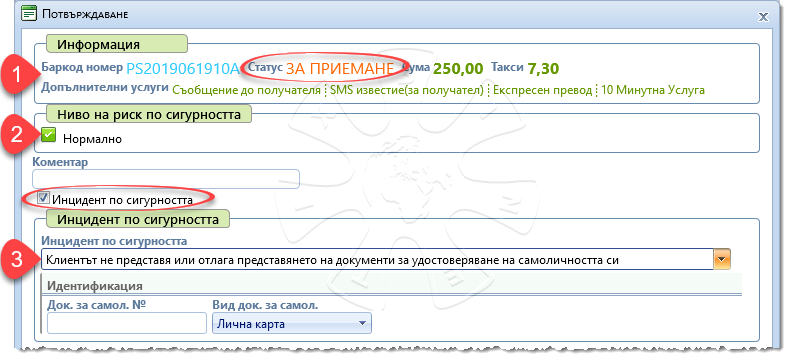
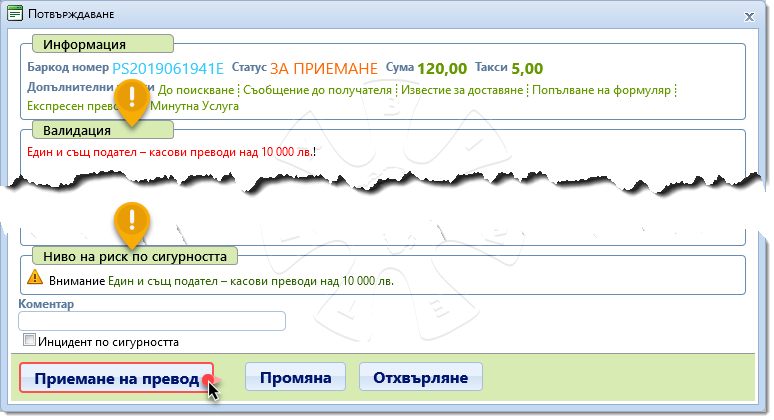
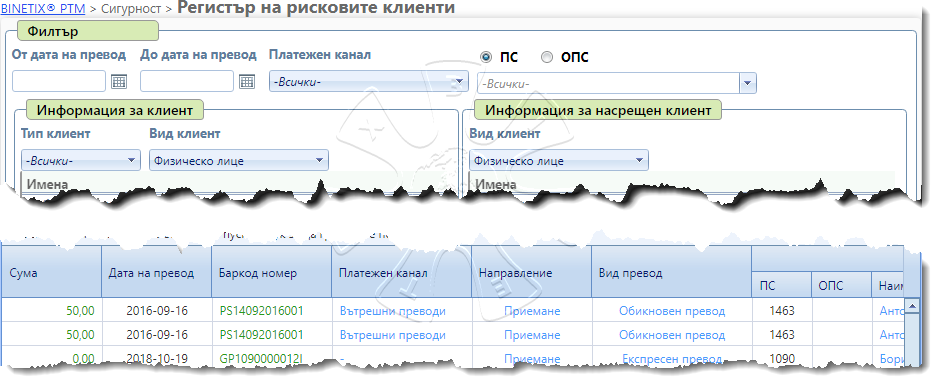
 Control of financial operations
Control of financial operations
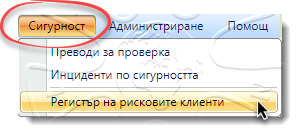
 Active incident management and reporting of suspicious persons and operations
Active incident management and reporting of suspicious persons and operations